Logs. ZyXEL Communications P-2612HW Series, P-2612HW-F1 -, P-2612HW
Add to my manuals547 Pages
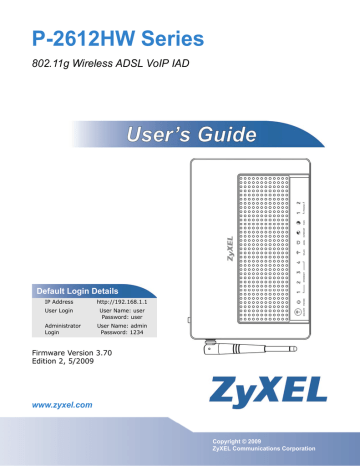
ZyXEL P-2612HW is a powerful and versatile networking device that offers a wide range of features and capabilities. With its 802.11g wireless connectivity, VoIP support, and ADSL modem, the P-2612HW is an ideal choice for home or small business users who need a reliable and affordable way to connect to the Internet and share files and resources. The device also features a built-in firewall and parental controls, making it a great choice for families with children.
advertisement
C H A P T E R 2 3
Logs
23.1 Overview
The web configurator allows you to choose which categories of events and/or alerts to have the ZyXEL Device log and then display the logs or have the ZyXEL
Device send them to an administrator (as e-mail) or to a syslog server.
23.1.1 What You Can Do in the Log Screens
• Use the View Log screen ( Section 23.2 on page 391 ) to see the logs for the
categories that you selected in the Log Settings screen.
• Use The Log Settings screen (
) to configure to where the ZyXEL Device is to send logs; the schedule for when the ZyXEL Device is to send the logs and which logs and/or immediate alerts the ZyXEL Device is to record.
23.1.2 What You Need To Know About Logs
Alerts and Logs
An alert is a type of log that warrants more serious attention. They include system errors, attacks (access control) and attempted access to blocked web sites. Some categories such as System Errors consist of both logs and alerts. You may differentiate them by their color in the View Log screen. Alerts display in red and logs display in black.
23.2 The View Log Screen
Click Maintenance > Logs to open the View Log screen. Use the View Log screen to see the logs for the categories that you selected in the Log Settings screen (see
).
391
P-2612HW Series User’s Guide
Chapter 23 Logs
Log entries in red indicate alerts. The log wraps around and deletes the old entries after it fills. Click a column heading to sort the entries. A triangle indicates ascending or descending sort order.
Figure 234 Maintenance > Logs > View Log
The following table describes the fields in this screen.
Table 129 Maintenance > Logs > View Log
LABEL
Display
DESCRIPTION
The categories that you select in the Log Settings screen display in the drop-down list box.
Select a category of logs to view; select All Logs to view logs from all of the log categories that you selected in the Log Settings page.
Email Log Now Click Email Log Now to send the log screen to the e-mail address specified in the Log Settings page (make sure that you have first filled in the E-mail Log Settings fields in Log Settings).
Refresh
Clear Log
#
Time
Message
Source
Destination
Notes
Click Refresh to renew the log screen.
Click Clear Log to delete all the logs.
This field is a sequential value and is not associated with a specific entry.
This field displays the time the log was recorded.
This field states the reason for the log.
This field lists the source IP address and the port number of the incoming packet.
This field lists the destination IP address and the port number of the incoming packet.
This field displays additional information about the log entry.
23.3 The Log Settings Screen
Use the Log Settings screen to configure to where the ZyXEL Device is to send logs; the schedule for when the ZyXEL Device is to send the logs and which logs
392
P-2612HW Series User’s Guide
Chapter 23 Logs and/or immediate alerts the ZyXEL Device is to record. See
To change your ZyXEL Device’s log settings, click Maintenance > Logs > Log
Settings. The screen appears as shown.
Alerts are e-mailed as soon as they happen. Logs may be e-mailed as soon as the log is full. Selecting many alert and/or log categories (especially Access Control) may result in many e-mails being sent.
Figure 235 Maintenance > Logs > Log Settings
P-2612HW Series User’s Guide
393
Chapter 23 Logs
The following table describes the fields in this screen.
Table 130 Maintenance > Logs > Log Settings
LABEL DESCRIPTION
E-mail Log Settings
Mail Server
Mail Subject
Send Log to
Enter the server name or the IP address of the mail server for the e-mail addresses specified below. If this field is left blank, logs and alert messages will not be sent via E-mail.
Type a title that you want to be in the subject line of the log e-mail message that the ZyXEL Device sends. Not all ZyXEL Device models have this field.
The ZyXEL Device sends logs to the e-mail address specified in this field.
If this field is left blank, the ZyXEL Device does not send logs via e-mail.
Send Alerts to Alerts are real-time notifications that are sent as soon as an event, such as a DoS attack, system error, or forbidden web access attempt occurs.
Enter the E-mail address where the alert messages will be sent. Alerts include system errors, attacks and attempted access to blocked web sites. If this field is left blank, alert messages will not be sent via E-mail.
Enable SMTP
Authentication
SMTP (Simple Mail Transfer Protocol) is the message-exchange standard for the Internet. SMTP enables you to move messages from one e-mail server to another.
User Name
Select the check box to activate SMTP authentication. If mail server authentication is needed but this feature is disabled, you will not receive the e-mail logs.
Enter the user name (up to 31 characters) (usually the user name of a mail account).
Password Enter the password associated with the user name above.
Log Schedule This drop-down menu is used to configure the frequency of log messages being sent as E-mail:
Day for
Sending Log
Time for
Sending Log
Clear log after sending mail
Syslog
Logging
Active
• Daily
• Weekly
• Hourly
• When Log is Full
• None.
If you select Weekly or Daily, specify a time of day when the E-mail should be sent. If you select Weekly, then also specify which day of the week the E-mail should be sent. If you select When Log is Full, an alert is sent when the log fills up. If you select None, no log messages are sent.
Use the drop down list box to select which day of the week to send the logs.
Enter the time of the day in 24-hour format (for example 23:00 equals
11:00 pm) to send the logs.
Select this to delete all the logs after the ZyXEL Device sends an E-mail of the logs.
The ZyXEL Device sends a log to an external syslog server.
Click Active to enable syslog logging.
394
P-2612HW Series User’s Guide
Chapter 23 Logs
Table 130 Maintenance > Logs > Log Settings
LABEL
Syslog IP
Address
DESCRIPTION
Enter the server name or IP address of the syslog server that will log the selected categories of logs.
Log Facility
Send
Immediate
Alert
Select a location from the drop down list box. The log facility allows you to log the messages to different files in the syslog server. Refer to the syslog server manual for more information.
Active Log and Alert
Log Select the categories of logs that you want to record.
Select log categories for which you want the ZyXEL Device to send E-mail alerts immediately.
Apply
Cancel
Click Apply to save your customized settings and exit this screen.
Click Cancel to return to the previously saved settings.
23.4 SMTP Error Messages
If there are difficulties in sending e-mail the following error message appears.
“SMTP action request failed. ret= ??". The “??"are described in the following table.
Table 131 SMTP Error Messages
-1 means ZyXEL Device out of socket
-2 means tcp SYN fail
-3 means smtp server OK fail
-4 means HELO fail
-5 means MAIL FROM fail
-6 means RCPT TO fail
-7 means DATA fail
-8 means mail data send fail
23.4.1 Example E-mail Log
An "End of Log" message displays for each mail in which a complete log has been sent. The following is an example of a log sent by e-mail.
• You may edit the subject title.
• The date format here is Day-Month-Year.
• The date format here is Month-Day-Year. The time format is Hour-Minute-
Second.
P-2612HW Series User’s Guide
395
Chapter 23 Logs
• "End of Log" message shows that a complete log has been sent.
Figure 236 E-mail Log Example
Subject:
Firewall Alert From
Date:
Fri, 07 Apr 2000 10:05:42
From:
To:
1|Apr 7 00 |From:192.168.1.1 To:192.168.1.255 |default policy |forward
| 09:54:03 |UDP src port:00520 dest port:00520 |<1,00> |
2|Apr 7 00 |From:192.168.1.131 To:192.168.1.255 |default policy |forward
| 09:54:17 |UDP src port:00520 dest port:00520 |<1,00> |
3|Apr 7 00 |From:192.168.1.6 To:10.10.10.10 |match |forward
| 09:54:19 |UDP src port:03516 dest port:00053 |<1,01> |
……………………………..{snip}…………………………………..
……………………………..{snip}…………………………………..
126|Apr 7 00 |From:192.168.1.1 To:192.168.1.255 |match |forward
| 10:05:00 |UDP src port:00520 dest port:00520 |<1,02> |
127|Apr 7 00 |From:192.168.1.131 To:192.168.1.255 |match |forward
| 10:05:17 |UDP src port:00520 dest port:00520 |<1,02> |
128|Apr 7 00 |From:192.168.1.1 To:192.168.1.255 |match |forward
| 10:05:30 |UDP src port:00520 dest port:00520 |<1,02> |
End of Firewall Log
23.5 Log Descriptions
This section provides descriptions of example log messages.
Table 132 System Maintenance Logs
LOG MESSAGE
Time calibration is successful
Time calibration failed
WAN interface gets IP: %s
DHCP client IP expired
DHCP server assigns %s
Successful WEB login
WEB login failed
Successful TELNET login
TELNET login failed
Successful FTP login
DESCRIPTION
The router has adjusted its time based on information from the time server.
The router failed to get information from the time server.
A WAN interface got a new IP address from the DHCP,
PPPoE, or dial-up server.
A DHCP client's IP address has expired.
The DHCP server assigned an IP address to a client.
Someone has logged on to the router's web configurator interface.
Someone has failed to log on to the router's web configurator interface.
Someone has logged on to the router via telnet.
Someone has failed to log on to the router via telnet.
Someone has logged on to the router via ftp.
396
P-2612HW Series User’s Guide
Chapter 23 Logs
Table 132 System Maintenance Logs (continued)
LOG MESSAGE
FTP login failed
NAT Session Table is Full!
Starting Connectivity
Monitor
DESCRIPTION
Someone has failed to log on to the router via ftp.
The maximum number of NAT session table entries has been exceeded and the table is full.
Starting Connectivity Monitor.
Time initialized by Daytime
Server
Time initialized by Time server
Time initialized by NTP server
The router got the time and date from the Daytime server.
The router got the time and date from the time server.
The router got the time and date from the NTP server.
Connect to Daytime server fail
Connect to Time server fail
Connect to NTP server fail
Too large ICMP packet has been dropped
Configuration Change: PC =
0x%x, Task ID = 0x%x
The router was not able to connect to the Daytime server.
The router was not able to connect to the Time server.
The router was not able to connect to the NTP server.
The router dropped an ICMP packet that was too large.
The router is saving configuration changes.
Successful SSH login
SSH login failed
Successful HTTPS login
HTTPS login failed
Someone has logged on to the router’s SSH server.
Someone has failed to log on to the router’s SSH server.
Someone has logged on to the router's web configurator interface using HTTPS protocol.
Someone has failed to log on to the router's web configurator interface using HTTPS protocol.
Table 133 System Error Logs
LOG MESSAGE
%s exceeds the max. number of session per host!
setNetBIOSFilter: calloc error readNetBIOSFilter: calloc error
WAN connection is down.
DESCRIPTION
This attempt to create a NAT session exceeds the maximum number of NAT session table entries allowed to be created per host.
The router failed to allocate memory for the NetBIOS filter settings.
The router failed to allocate memory for the NetBIOS filter settings.
A WAN connection is down. You cannot access the network through this interface.
P-2612HW Series User’s Guide
397
Chapter 23 Logs
Table 134 Access Control Logs
LOG MESSAGE
Firewall default policy: [ TCP |
UDP | IGMP | ESP | GRE | OSPF ]
<Packet Direction>
Firewall rule [NOT] match:[ TCP
| UDP | IGMP | ESP | GRE | OSPF
] <Packet Direction>, <rule:%d>
DESCRIPTION
Attempted TCP/UDP/IGMP/ESP/GRE/OSPF access matched the default policy and was blocked or forwarded according to the default policy’s setting.
Attempted TCP/UDP/IGMP/ESP/GRE/OSPF access matched (or did not match) a configured firewall rule (denoted by its number) and was blocked or forwarded according to the rule.
The firewall allowed a triangle route session to pass through.
Triangle route packet forwarded:
[ TCP | UDP | IGMP | ESP | GRE |
OSPF ]
Packet without a NAT table entry blocked: [ TCP | UDP | IGMP |
ESP | GRE | OSPF ]
Router sent blocked web site message: TCP
The router blocked a packet that didn't have a corresponding NAT table entry.
The router sent a message to notify a user that the router blocked access to a web site that the user requested.
Table 135 TCP Reset Logs
LOG MESSAGE
Under SYN flood attack, sent TCP RST
Exceed TCP MAX incomplete, sent TCP RST
Peer TCP state out of order, sent TCP RST
Firewall session time out, sent TCP RST
DESCRIPTION
The router sent a TCP reset packet when a host was under a SYN flood attack (the TCP incomplete count is per destination host.)
The router sent a TCP reset packet when the number of
TCP incomplete connections exceeded the user configured threshold. (the TCP incomplete count is per destination host.) Note: Refer to TCP Maximum Incomplete in the
Firewall Attack Alerts screen.
The router sent a TCP reset packet when a TCP connection state was out of order.Note: The firewall refers to RFC793 Figure 6 to check the TCP state.
The router sent a TCP reset packet when a dynamic firewall session timed out.Default timeout values:ICMP idle timeout (s): 60UDP idle timeout (s): 60TCP connection (three way handshaking) timeout (s): 30TCP
FIN-wait timeout (s): 60TCP idle (established) timeout
(s): 3600
398
P-2612HW Series User’s Guide
Chapter 23 Logs
Table 135 TCP Reset Logs (continued)
LOG MESSAGE
Exceed MAX incomplete, sent TCP RST
Access block, sent TCP
RST
DESCRIPTION
The router sent a TCP reset packet when the number of incomplete connections (TCP and UDP) exceeded the user-configured threshold. (Incomplete count is for all
TCP and UDP connections through the firewall.)Note:
When the number of incomplete connections (TCP + UDP)
> “Maximum Incomplete High”, the router sends TCP RST packets for TCP connections and destroys TOS (firewall dynamic sessions) until incomplete connections <
“Maximum Incomplete Low”.
The router sends a TCP RST packet and generates this log if you turn on the firewall TCP reset mechanism (via CI command: "sys firewall tcprst").
Table 136 Packet Filter Logs
LOG MESSAGE
[ TCP | UDP | ICMP | IGMP |
Generic ] packet filter matched (set: %d, rule: %d)
DESCRIPTION
Attempted access matched a configured filter rule
(denoted by its set and rule number) and was blocked or forwarded according to the rule.
For type and code details, see
.
Table 137 ICMP Logs
LOG MESSAGE
Firewall default policy: ICMP
<Packet Direction>, <type:%d>,
<code:%d>
Firewall rule [NOT] match: ICMP
<Packet Direction>, <rule:%d>,
<type:%d>, <code:%d>
Triangle route packet forwarded:
ICMP
Packet without a NAT table entry blocked: ICMP
Unsupported/out-of-order ICMP:
ICMP
Router reply ICMP packet: ICMP
DESCRIPTION
ICMP access matched the default policy and was blocked or forwarded according to the user's setting.
ICMP access matched (or didn’t match) a firewall rule (denoted by its number) and was blocked or forwarded according to the rule.
The firewall allowed a triangle route session to pass through.
The router blocked a packet that didn’t have a corresponding NAT table entry.
The firewall does not support this kind of ICMP packets or the ICMP packets are out of order.
The router sent an ICMP reply packet to the sender.
P-2612HW Series User’s Guide
399
Chapter 23 Logs
Table 138 CDR Logs
LOG MESSAGE board %d line %d channel %d, call %d, %s C01 Outgoing Call dev=%x ch=%x %s
DESCRIPTION
The router received the setup requirements for a call.
“call” is the reference (count) number of the call.
“dev” is the device type (3 is for dial-up, 6 is for
PPPoE, 10 is for PPTP). "channel" or “ch” is the call channel ID.For example,"board 0 line 0 channel 0, call
3, C01 Outgoing Call dev=6 ch=0 "Means the router has dialed to the PPPoE server 3 times.
The PPPoE, PPTP or dial-up call is connected.
board %d line %d channel %d, call %d, %s C02 OutCall
Connected %d %s board %d line %d channel %d, call %d, %s C02 Call
Terminated
The PPPoE, PPTP or dial-up call was disconnected.
Table 139 PPP Logs
LOG MESSAGE DESCRIPTION ppp:LCP Starting
The PPP connection’s Link Control Protocol stage has started.
ppp:LCP Opening
The PPP connection’s Link Control Protocol stage is opening.
ppp:CHAP Opening
The PPP connection’s Challenge Handshake Authentication Protocol stage is opening.
ppp:IPCP
Starting
The PPP connection’s Internet Protocol Control Protocol stage is starting.
ppp:IPCP Opening
The PPP connection’s Internet Protocol Control Protocol stage is opening.
ppp:LCP Closing
The PPP connection’s Link Control Protocol stage is closing.
ppp:IPCP Closing
The PPP connection’s Internet Protocol Control Protocol stage is closing.
Table 140 UPnP Logs
LOG MESSAGE
UPnP pass through Firewall
DESCRIPTION
UPnP packets can pass through the firewall.
Table 141 Content Filtering Logs
LOG MESSAGE
%s: block keyword
%s
DESCRIPTION
The content of a requested web page matched a user defined keyword.
The system forwarded web content.
400
P-2612HW Series User’s Guide
Chapter 23 Logs
For type and code details, see
.
Table 142 Attack Logs
LOG MESSAGE attack [ TCP | UDP | IGMP
| ESP | GRE | OSPF ]
DESCRIPTION
The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF attack.
The firewall detected an ICMP attack.
attack ICMP (type:%d, code:%d) land [ TCP | UDP | IGMP |
ESP | GRE | OSPF ]
The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF land attack.
The firewall detected an ICMP land attack.
land ICMP (type:%d, code:%d) ip spoofing - WAN [ TCP |
UDP | IGMP | ESP | GRE |
OSPF ]
The firewall detected an IP spoofing attack on the WAN port.
ip spoofing - WAN ICMP
(type:%d, code:%d)
The firewall detected an ICMP IP spoofing attack on the
WAN port.
The firewall detected an ICMP echo attack. icmp echo : ICMP
(type:%d, code:%d) syn flood TCP ports scan TCP teardrop TCP teardrop UDP teardrop ICMP (type:%d, code:%d)
The firewall detected a TCP syn flood attack.
The firewall detected a TCP port scan attack.
The firewall detected a TCP teardrop attack.
The firewall detected an UDP teardrop attack.
The firewall detected an ICMP teardrop attack. illegal command TCP
NetBIOS TCP ip spoofing - no routing entry [ TCP | UDP | IGMP
| ESP | GRE | OSPF ]
The firewall detected a TCP illegal command attack.
The firewall detected a TCP NetBIOS attack.
The firewall classified a packet with no source routing entry as an IP spoofing attack.
ip spoofing - no routing entry ICMP (type:%d, code:%d)
The firewall classified an ICMP packet with no source routing entry as an IP spoofing attack.
vulnerability ICMP
(type:%d, code:%d) traceroute ICMP (type:%d, code:%d)
The firewall detected an ICMP vulnerability attack.
The firewall detected an ICMP traceroute attack.
Table 143 802.1X Logs
LOG MESSAGE
RADIUS accepts user.
RADIUS rejects user. Pls check
RADIUS Server.
User logout because of session timeout expired.
DESCRIPTION
A user was authenticated by the RADIUS Server.
A user was not authenticated by the RADIUS
Server. Please check the RADIUS Server.
The router logged out a user whose session expired.
P-2612HW Series User’s Guide
401
Chapter 23 Logs
Table 143 802.1X Logs (continued)
LOG MESSAGE
User logout because of user deassociation.
DESCRIPTION
The router logged out a user who ended the session.
User logout because of no authentication response from user.
The router logged out a user from which there was no authentication response.
User logout because of idle timeout expired.
The router logged out a user whose idle timeout period expired.
A user logged out.
User logout because of user request.
No response from RADIUS. Pls check RADIUS Server.
Use RADIUS to authenticate user.
There is no response message from the RADIUS server, please check the RADIUS server.
The RADIUS server is operating as the authentication server.
No Server to authenticate user.
There is no authentication server to authenticate a user.
Table 144 ACL Setting Notes
PACKET
DIRECTION
(L to W)
(W to L)
(L to L/ZyXEL
Device)
(W to W/ZyXEL
Device)
DIRECTION
LAN to WAN
WAN to LAN
LAN to LAN/
ZyXEL Device
WAN to WAN/
ZyXEL Device
DESCRIPTION
ACL set for packets traveling from the LAN to the
WAN.
ACL set for packets traveling from the WAN to the
LAN.
ACL set for packets traveling from the LAN to the
LAN or the ZyXEL Device.
ACL set for packets traveling from the WAN to the
WAN or the ZyXEL Device.
Table 145 ICMP Notes
TYPE
0
3
CODE DESCRIPTION
Echo Reply
0
0
1
2
3
4
5
Echo reply message
Destination Unreachable
Net unreachable
Host unreachable
Protocol unreachable
Port unreachable
A packet that needed fragmentation was dropped because it was set to Don't Fragment (DF)
Source route failed
402
P-2612HW Series User’s Guide
Chapter 23 Logs
Table 145 ICMP Notes (continued)
TYPE
4
5
8
11
12
13
14
15
16
CODE DESCRIPTION
Source Quench
0
0
1
2
3
0
0
1
0
0
0
0
0
A gateway may discard internet datagrams if it does not have the buffer space needed to queue the datagrams for output to the next network on the route to the destination network.
Redirect
Redirect datagrams for the Network
Redirect datagrams for the Host
Redirect datagrams for the Type of Service and Network
Redirect datagrams for the Type of Service and Host
Echo
Echo message
Time Exceeded
Time to live exceeded in transit
Fragment reassembly time exceeded
Parameter Problem
Pointer indicates the error
Timestamp
Timestamp request message
Timestamp Reply
Timestamp reply message
Information Request
Information request message
Information Reply
Information reply message
Table 146 Syslog Logs
LOG MESSAGE
<Facility*8 + Severity>Mon dd hr:mm:ss hostname src="<srcIP:srcPort>" dst="<dstIP:dstPort>" msg="<msg>" note="<note>" devID="<mac address last three numbers>" cat="<category>
DESCRIPTION
"This message is sent by the system ("RAS" displays as the system name if you haven’t configured one) when the router generates a syslog. The facility is defined in the web MAIN
MENU->LOGS->Log Settings page. The severity is the log’s syslog class. The definition of messages and notes are defined in the various log charts throughout this appendix. The “devID” is the last three characters of the MAC address of the router’s
LAN port. The “cat” is the same as the category in the router’s logs.
P-2612HW Series User’s Guide
403
Chapter 23 Logs
Table 147 SIP Logs
LOG MESSAGE
SIP Registration Success by SIP:SIP Phone Number
SIP Registration Fail by
SIP:SIP Phone Number
SIP UnRegistration
Success by SIP:SIP Phone
Number
SIP UnRegistration Fail by SIP:SIP Phone Number
DESCRIPTION
The listed SIP account was successfully registered with a
SIP register server.
An attempt to register the listed SIP account with a SIP register server was not successful.
The listed SIP account’s registration was deleted from the
SIP register server.
An attempt to delete the listed SIP account’s registration from the SIP register server failed.
Table 148 RTP Logs
LOG MESSAGE
Error, RTP init fail
Error, Call fail: RTP connect fail
Error, RTP connection cannot close
DESCRIPTION
The initialization of an RTP session failed.
A VoIP phone call failed because the RTP session could not be established.
The termination of an RTP session failed.
Table 149 FSM Logs: Caller Side
LOG MESSAGE
VoIP Call Start Ph[Phone
Port Number] <- Outgoing
Call Number
DESCRIPTION
Someone used a phone connected to the listed phone port to initiate a VoIP call to the listed destination.
VoIP Call Established
Ph[Phone Port] ->
Outgoing Call Number
Someone used a phone connected to the listed phone port to make a VoIP call to the listed destination.
VoIP Call End Phone[Phone
Port]
A VoIP phone call made from a phone connected to the listed phone port has terminated.
404
P-2612HW Series User’s Guide
Chapter 23 Logs
Table 150 FSM Logs: Callee Side
LOG MESSAGE
VoIP Call Start from
SIP[SIP Port Number]
VoIP Call Established
Ph[Phone Port] <-
Outgoing Call Number
DESCRIPTION
A VoIP phone call came to the ZyXEL Device from the listed SIP number.
A VoIP phone call was set up from the listed SIP number to the ZyXEL Device.
VoIP Call End Phone[Phone
Port]
A VoIP phone call that came into the ZyXEL Device has terminated.
The following table shows RFC-2408 ISAKMP payload types that the log displays.
Please refer to RFC 2408 for detailed information on each type.
Table 151 RFC-2408 ISAKMP Payload Types
LOG DISPLAY
SA
PROP
TRANS
KE
ID
CER
CER_REQ
HASH
SIG
NONCE
NOTFY
DEL
VID
PAYLOAD TYPE
Security Association
Proposal
Transform
Key Exchange
Identification
Certificate
Certificate Request
Hash
Signature
Nonce
Notification
Delete
Vendor ID
P-2612HW Series User’s Guide
405
Chapter 23 Logs
406
P-2612HW Series User’s Guide
advertisement
* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Key Features
- 802.11g wireless connectivity for fast and reliable wireless networking
- VoIP support for making and receiving phone calls over the Internet
- ADSL modem for connecting to the Internet over a standard phone line
- Built-in firewall for protecting your network from unauthorized access
- Parental controls for restricting access to inappropriate content
- Easy-to-use web-based interface for configuring and managing the device
- Compact and stylish design that fits easily into any home or office environment
Related manuals
Frequently Answers and Questions
How do I connect the P-2612HW to my computer?
How do I configure the P-2612HW?
How do I troubleshoot problems with the P-2612HW?
advertisement
Table of contents
- 1 P-2612HW Series
- 3 About This User's Guide
- 5 Document Conventions
- 7 Safety Warnings
- 9 Contents Overview
- 11 Table of Contents
- 23 Introduction
- 25 Introducing the ZyXEL Device
- 25 1.1 Overview
- 25 1.1.1 Internet Access
- 27 1.1.2 VoIP Features
- 27 1.2 Ways to Manage the ZyXEL Device
- 28 1.3 Good Habits for Managing the ZyXEL Device
- 28 1.4 LEDs (Lights)
- 29 1.5 The RESET Button
- 30 1.6 The WLAN Button
- 31 Introducing the Web Configurator
- 31 2.1 Web Configurator Overview
- 31 2.1.1 Accessing the Web Configurator
- 33 2.2 Web Configurator Main Screen
- 33 2.2.1 Title Bar
- 34 2.2.2 Navigation Panel
- 38 2.2.3 Main Window
- 38 2.2.4 Status Bar
- 39 Wizards
- 39 3.1 Overview
- 39 3.2 Internet Access Wizard Setup
- 42 3.2.1 Manual Configuration
- 46 3.3 Wireless Connection Wizard Setup
- 49 3.3.1 Manually Assign a WPA-PSK key
- 50 3.3.2 Manually Assign a WEP Key
- 51 3.4 VoIP Setup Wizard
- 52 3.4.1 SIP Settings
- 53 3.4.2 Registration Complete
- 57 Tutorial
- 57 4.1 Overview
- 57 4.2 How to Set up a Wireless Network
- 57 4.2.1 Example Parameters
- 58 4.2.2 Configuring the AP
- 60 4.2.3 Configuring the Wireless Client
- 66 4.3 Using NAT with Multiple Public IP Addresses
- 66 4.3.1 Example Parameters and Scenario
- 67 4.3.2 Configuring the WAN Connection with a Static IP Address
- 70 4.3.3 Public IP Address Mapping
- 74 4.3.4 Forwarding Traffic from the WAN to a Local Computer
- 75 4.3.5 Allow WAN-to-LAN Traffic through the Firewall
- 83 4.3.6 Testing the Connections
- 83 4.4 Using NAT with Multiple Game Players
- 84 4.5 How to Make a VoIP Call
- 84 4.5.1 VoIP Calls With a Registered SIP Account
- 87 Advanced
- 89 Status Screens
- 89 5.1 Status Screen
- 94 5.2 Any IP Table
- 94 5.3 WLAN Status
- 95 5.4 Packet Statistics
- 97 5.5 VoIP Statistics
- 99 WAN Setup
- 99 6.1 Overview
- 99 6.1.1 What You Can Do in the WAN Screens
- 100 6.1.2 What You Need to Know About WAN
- 100 6.1.3 Before You Begin
- 101 6.2 The Internet Access Setup Screen
- 104 6.2.1 Advanced Internet Access Setup
- 105 6.3 The More Connections Screen
- 107 6.3.1 More Connections Edit
- 110 6.3.2 Configuring More Connections Advanced Setup
- 112 6.4 The WAN Backup Setup Screen
- 113 6.5 WAN Technical Reference
- 113 6.5.1 Encapsulation
- 115 6.5.2 Multiplexing
- 115 6.5.3 VPI and VCI
- 115 6.5.4 IP Address Assignment
- 116 6.5.5 Nailed-Up Connection (PPP)
- 116 6.5.6 NAT
- 116 6.5.7 Metric
- 117 6.5.8 Traffic Shaping
- 119 6.6 Traffic Redirect
- 121 LAN Setup
- 121 7.1 Overview
- 121 7.1.1 What You Can Do in the LAN Screens
- 122 7.1.2 What You Need To Know About LAN
- 122 7.1.3 Before You Begin
- 122 7.2 The LAN IP Screen
- 124 7.2.1 The Advanced LAN Setup Screen
- 125 7.2.2 Configuring the Advanced LAN Setup Screen
- 126 7.3 The LAN Client List Screen
- 128 7.4 The LAN IP Alias Screen
- 129 7.5 LAN Technical Reference
- 130 7.5.1 LANs, WANs and the ZyXEL Device
- 130 7.5.2 DHCP Setup
- 130 7.5.3 DNS Server Addresses
- 131 7.5.4 TCP/IP
- 132 7.5.5 RIP Setup
- 133 7.5.6 Multicast
- 133 7.5.7 Any IP
- 137 Wireless LAN
- 137 8.1 Overview
- 137 8.1.1 What You Can Do in the Wireless LAN Screens
- 138 8.1.2 What You Need to Know About Wireless
- 140 8.1.3 Before You Start
- 140 8.2 AP Screen
- 142 8.2.1 No Security
- 143 8.2.2 WEP Encryption
- 144 8.2.3 WPA(2)-PSK
- 146 8.2.4 WPA(2) Authentication Screen
- 148 8.2.5 Wireless LAN Advanced Setup
- 149 8.3 More AP Screen
- 150 8.3.1 More AP Edit
- 151 8.4 MAC Filter
- 152 8.5 WPS
- 153 8.6 WPS Station
- 154 8.7 WDS Screen
- 156 8.8 Scheduling Screen
- 157 8.9 Wireless LAN Technical Reference
- 157 8.9.1 Additional Wireless Terms
- 157 8.9.2 Wireless Security Overview
- 160 8.9.3 MBSSID
- 160 8.9.4 Wireless Distribution System (WDS)
- 161 8.9.5 WiFi Protected Setup
- 169 Network Address Translation (NAT)
- 169 9.1 Overview
- 169 9.1.1 What You Can Do in the NAT Screens
- 169 9.1.2 What You Need To Know About NAT
- 170 9.2 NAT General Setup
- 172 9.3 Port Forwarding
- 173 9.3.1 Configuring the Port Forwarding Screen
- 175 9.3.2 Port Forwarding Rule Edit
- 176 9.4 Address Mapping
- 177 9.4.1 Address Mapping Rule Edit
- 178 9.4.2 SIP ALG
- 179 9.5 NAT Technical Reference
- 179 9.5.1 NAT Definitions
- 180 9.5.2 What NAT Does
- 180 9.5.3 How NAT Works
- 182 9.5.4 NAT Application
- 182 9.5.5 NAT Mapping Types
- 185 Voice
- 185 10.1 Overview
- 185 10.1.1 What You Can Do in the VoIP Screens
- 186 10.1.2 What You Need to Know About VoIP
- 187 10.1.3 Before You Begin
- 187 10.2 The SIP Settings Screen
- 190 10.3 The Advanced SIP Setup Screen
- 193 10.4 The SIP QoS Screen
- 194 10.5 The Analog Phone Screen
- 194 10.6 The Advanced Analog Phone Setup Screen
- 195 10.6.1 Configuring the Advanced Analog Phone Screen
- 197 10.7 The Phone Settings Ext. Table Screen
- 198 10.8 The Common Phone Settings Screen
- 199 10.9 The Phone Region Screen
- 200 10.10 The Speed Dial Screen
- 203 10.11 Incoming Call Policy Screen
- 205 10.12 SIP Prefix Screen
- 206 10.13 SIP Technical Reference
- 206 10.13.1 VoIP
- 206 10.13.2 SIP
- 215 10.13.3 Quality of Service (QoS)
- 216 10.13.4 Phone Services Overview
- 221 Phone Usage
- 221 11.1 Overview
- 221 11.2 Dialing a Telephone Number
- 221 11.3 Using Speed Dial to Dial a Telephone Number
- 221 11.4 Using Call Park and Pickup
- 222 11.5 Checking the ZyXEL Device’s IP Address
- 222 11.6 Auto Provisioning and Auto Firmware Upgrade
- 223 11.7 Phone Services Overview
- 223 11.7.1 The Flash Key
- 223 11.7.2 Europe Type Supplementary Phone Services
- 225 11.7.3 USA Type Supplementary Services
- 227 11.8 Phone Functions Summary
- 229 Firewall
- 229 12.1 Overview
- 229 12.1.1 What You Can Do in the Firewall Screens
- 230 12.1.2 What You Need to Know About Firewall
- 230 12.1.3 Firewall Rule Setup Example
- 234 12.2 The Firewall General Screen
- 236 12.3 The Firewall Rule Screen
- 237 12.3.1 Configuring Firewall Rules
- 240 12.3.2 Customized Services
- 241 12.3.3 Configuring a Customized Service
- 241 12.4 The Firewall Threshold Screen
- 242 12.4.1 Threshold Values
- 243 12.4.2 Configuring Firewall Thresholds
- 245 12.5 Firewall Technical Reference
- 245 12.5.1 Firewall Rules Overview
- 246 12.5.2 Guidelines For Enhancing Security With Your Firewall
- 247 12.5.3 Security Considerations
- 247 12.5.4 Triangle Route
- 251 Content Filtering
- 251 13.1 Overview
- 251 13.1.1 What You Can Do in the Content Filter Screens
- 251 13.1.2 What You Need to Know About Content Filtering
- 251 13.1.3 Before You Begin
- 252 13.1.4 Content Filtering Example
- 254 13.2 The Keyword Screen
- 255 13.3 The Schedule Screen
- 256 13.4 The Trusted Screen
- 257 VPN
- 257 14.1 Overview
- 257 14.1.1 What You Can Do in the VPN Screens
- 258 14.1.2 What You Need to Know About IPSec VPN
- 259 14.1.3 Before You Begin
- 260 14.2 VPN Setup Screen
- 262 14.3 The VPN Edit Screen
- 268 14.4 Configuring Advanced IKE Settings
- 271 14.5 Manual Key Setup
- 271 14.5.1 Security Parameter Index (SPI)
- 272 14.6 Configuring Manual Key
- 275 14.7 Viewing SA Monitor
- 277 14.8 Configuring VPN Global Setting
- 277 14.9 IPSec VPN Technical Reference
- 278 14.9.1 IPSec Architecture
- 278 14.9.2 IPSec and NAT
- 279 14.9.3 VPN, NAT, and NAT Traversal
- 281 14.9.4 Encapsulation
- 282 14.9.5 IKE Phases
- 283 14.9.6 Negotiation Mode
- 283 14.9.7 Keep Alive
- 283 14.9.8 Remote DNS Server
- 284 14.9.9 ID Type and Content
- 286 14.9.10 Pre-Shared Key
- 286 14.9.11 Diffie-Hellman (DH) Key Groups
- 286 14.9.12 Telecommuter VPN/IPSec Examples
- 291 Certificates
- 291 15.1 Overview
- 291 15.1.1 What You Can Do in the Certificate Screens
- 291 15.1.2 What You Need to Know About Certificates
- 293 15.1.3 Verifying a Certificate
- 295 15.2 My Certificates
- 297 15.3 My Certificate Details
- 301 15.3.1 Using the My Certificate Import Screen
- 301 15.4 My Certificate Create
- 304 15.5 Trusted CAs
- 306 15.6 Trusted CA Import
- 307 15.7 Trusted CA Details
- 311 15.8 Trusted Remote Hosts
- 312 15.9 Trusted Remote Host Certificate Details
- 315 15.10 Trusted Remote Hosts Import
- 316 15.11 Directory Servers
- 318 15.12 Directory Server Add and Edit
- 321 Static Route
- 321 16.1 Overview
- 321 16.1.1 What You Can Do in the Static Route Screens
- 322 16.2 Configuring Static Route
- 323 16.2.1 Static Route Edit
- 325 802.1Q/1P
- 325 17.1 Overview
- 325 17.1.1 What You Can Do in the 802.1Q/1P Screens
- 325 17.1.2 What You Need to Know About 802.1Q/1P
- 327 17.1.3 802.1Q/1P Example
- 332 17.2 The 802.1Q/1P Group Setting Screen
- 333 17.2.1 Editing 802.1Q/1P Group Setting
- 335 17.3 The 802.1Q/1P Port Setting Screen
- 337 Quality of Service (QoS)
- 337 18.1 Overview
- 337 18.1.1 What You Can Do in the QoS Screens
- 338 18.1.2 What You Need to Know About QoS
- 338 18.1.3 QoS Class Setup Example
- 341 18.2 The QoS General Screen
- 343 18.3 The Class Setup Screen
- 345 18.3.1 The Class Configuration Screen
- 349 18.4 The QoS Monitor Screen
- 349 18.5 QoS Technical Reference
- 350 18.5.1 IEEE 802.1Q Tag
- 350 18.5.2 IP Precedence
- 350 18.5.3 DiffServ
- 351 18.5.4 Automatic Priority Queue Assignment
- 353 Dynamic DNS Setup
- 353 19.1 Overview
- 353 19.1.1 What You Can Do in the DDNS Screen
- 353 19.1.2 What You Need To Know About DDNS
- 354 19.2 Configuring Dynamic DNS
- 357 Remote Management Configuration
- 357 20.1 Overview
- 358 20.1.1 What You Can Do in the Remote Management Screens
- 358 20.1.2 What You Need to Know About Remote Management
- 359 20.2 The WWW Screen
- 360 20.3 The Telnet Screen
- 361 20.4 The FTP Screen
- 362 20.5 The SNMP Screen
- 364 20.5.1 Configuring SNMP
- 365 20.6 The DNS Screen
- 366 20.7 The ICMP Screen
- 369 Universal Plug-and-Play (UPnP)
- 369 21.1 Overview
- 369 21.1.1 What You Can Do in the UPnP Screen
- 369 21.1.2 What You Need to Know About UPnP
- 371 21.2 The UPnP Screen
- 371 21.3 Installing UPnP in Windows Example
- 375 21.4 Using UPnP in Windows XP Example
- 383 Maintenance, Troubleshooting and Specifications
- 385 System
- 385 22.1 Overview
- 385 22.1.1 What You Can Do in the System Settings Screens
- 385 22.1.2 What You Need to Know About System Settings
- 386 22.2 The General Screen
- 388 22.3 The Time Setting Screen
- 391 Logs
- 391 23.1 Overview
- 391 23.1.1 What You Can Do in the Log Screens
- 391 23.1.2 What You Need To Know About Logs
- 391 23.2 The View Log Screen
- 392 23.3 The Log Settings Screen
- 395 23.4 SMTP Error Messages
- 395 23.4.1 Example E-mail Log
- 396 23.5 Log Descriptions
- 407 Call History
- 407 24.1 Overview
- 407 24.1.1 What You Can Do in the Call History Screens
- 407 24.2 Call History Summary Screen
- 408 24.3 Viewing the Call History
- 409 24.4 Configuring Call History Settings
- 413 Tools
- 413 25.1 Overview
- 413 25.1.1 What You Can Do in the Tool Screens
- 413 25.1.2 What You Need To Know About Tools
- 415 25.1.3 Before You Begin
- 415 25.1.4 Tool Examples
- 420 25.2 Firmware Upgrade Screen
- 423 25.3 The Configuration Screen
- 425 25.3.1 Reset to Factory Defaults
- 426 25.4 Restart
- 426 25.5 Using FTP or TFTP to Back Up Configuration
- 426 25.5.1 Using the FTP Commands to Back Up Configuration
- 427 25.5.2 FTP Command Configuration Backup Example
- 427 25.5.3 Configuration Backup Using GUI-based FTP Clients
- 427 25.5.4 Backup Configuration Using TFTP
- 428 25.5.5 TFTP Command Configuration Backup Example
- 429 25.5.6 Configuration Backup Using GUI-based TFTP Clients
- 429 25.6 Using FTP or TFTP to Restore Configuration
- 430 25.6.1 Restore Using FTP Session Example
- 430 25.7 FTP and TFTP Firmware and Configuration File Uploads
- 430 25.7.1 FTP File Upload Command from the DOS Prompt Example
- 431 25.7.2 FTP Session Example of Firmware File Upload
- 431 25.7.3 TFTP File Upload
- 432 25.7.4 TFTP Upload Command Example
- 433 Diagnostic
- 433 26.1 Overview
- 433 26.1.1 What You Can Do in the Diagnostic Screens
- 433 26.2 The General Diagnostic Screen
- 434 26.3 The DSL Line Diagnostic Screen
- 437 Troubleshooting
- 437 27.1 Overview
- 437 27.2 Power, Hardware Connections, and LEDs
- 438 27.3 ZyXEL Device Access and Login
- 440 27.4 Internet Access
- 441 27.5 Phone Calls and VoIP
- 442 27.6 Multiple SIP Accounts
- 442 27.6.1 Outgoing Calls
- 443 27.6.2 Incoming Calls
- 445 Product Specifications
- 457 Appendices and Index
- 459 Setting Up Your Computer’s IP Address
- 485 Pop-up Windows, JavaScripts and Java Permissions
- 495 IP Addresses and Subnetting
- 507 Wireless LANs
- 531 Common Services
- 535 Legal Information
- 537 Index